When it comes to security companies most of what we see is quite bad. Most of them don’t have a good understanding of security, sell products and services that can’t do what they claim they can, or are some combination of both of those things. Sucuri Security is one of the worst companies we have seen and would fall in to that last category. We have been hired on quite a few occasions to re-clean websites they previously hired to clean, for which they failed to basic parts of the cleanup – like determining how the website was hacked – that if done, should have prevented the website from being re-hacked in the first place. Among things we have seen, there was the recent situation we came across where we found that they were helping to put WordPress websites at greater risk of being hacked.
That isn’t just our perspective, last week someone contacted us wanted to know if we knew a good alternative to Sucuri due to this litany problems they had with them:
I’ve been using Sucuri for about 5-6 months and it’s been the worst experience I’ve had with a service provider that I can remember. CloudProxy throws false positives all the time, and I explicitly asked them to remove it from one of our 5 sites multiple times and support ignored the request. The support has been bad from day one–beyond belief bad–not just in this instance but with nearly all the tickets I’ve opened.
Three years ago we discussed their SiteCheck security scanner’s poor quality and something we ran across the other day shows that it hasn’t gotten better, but in the meantime they have turned up the fear factor to try to scare people into using their service.
While we were looking too see if anyone else had discussed a false report of a vulnerability in WordPress 4.2.2, we can across a mention that a security company was running a vulnerable version of the Apache HTTP server on their website. That would be interesting if it was true. Following the link on that post brought us to this page on Sucuri’s SiteCheck:
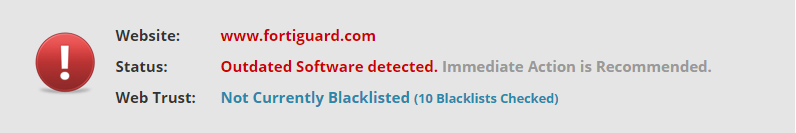
A quick check showed that Sucuri was providing misleading information, we’ll explain that in second, but first let’s look at their rather scary warnings that came along with that bad information. First they warn “Outdated Software detected. Immediate Action is Recommended.”:
Then they warn of a “High” severity issue due to the website being outdated. and recommend to “PATCH AND PROTECT With Sucuri Firewall”:
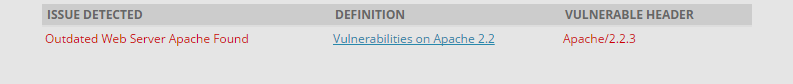
Then they warn that an “Outdated Web Server Apache Found”:
They are a couple of major problems with this, first if the Apache HTTP Server version was actually outdated the solution would be to update it, not buy some security service they provide. Only in small text at the bottom do they suggest that “You can contact your host about it and ask them to update for you”:
Their claim that their CloudProxy service can automatically update the software is simply untrue.
The bigger problem is that Sucuri has no idea if the Apache HTTP server is in fact outdated in this instance and therefore if the “High” severity issue actually exists. To explain this let’s start by taking a look at a second screenshot, this time of our Server Details extension for Chrome on the same website:
You can see it also identifies the website as using version 2.2.3 of the Apache HTTP Server, but it doesn’t label it as being outdated (despite that being a capability of the extension). The reason it doesn’t label it as being outdated is due to the second piece of information, that the server is running CentOS 5. The CentOS operating system is based on Red Hat Enterprise Linux (RHEL), which means that instead of introducing new versions of included software when a security fix is released they backport the security fix to the existing version. That means that while that server is using an outdated version of the Apache HTTP Server, it isn’t necessarily outdated in a security sense. If Sucuri Security did in fact have the security expertise they claim to have, they would know about this and properly handled this situation.
Now you might be wondering how hard it would have been for them to check for this type of situation before showing such dire warnings. They way we get the information for our extension and how Sucuri probably get their data is to look at the Server HTTP header. For this website it is this:
Apache/2.2.3 (CentOS)
CentOS is one of three words in it, so it isn’t hard to detect. (We are able to say the website is running version 5 of CentOS based on the Apache HTTP Server version identified in that.)