Back in May of 2015 we had put out a post discussing the fact that the web host CloudAccess.net was storing FTP/SFTP/SSH passwords in non-hashed form. Here is how we explained why storing them in hashed form was important, at that time:
One of the measures that needs to be taken is to store passwords as securely as possible, which means storing them in hashed form. You can think of a password hashing as one-way encryption. That is, the data is encrypted, but it cannot be decrypted, so the underlying password is not retrievable in normal circumstances. With this type of password storage when someone tries to log in the password they input is hashed and then compared with the stored password hash to see if they are the same. With hashed passwords even if someone gets access to the stored passwords it would be difficult for them to do anything with them, since they would first have to crack the hashes.
Then back in January we received a comment on the post apparently from the CEO of CloudAccess.net:
I represent CloudAccess.net, the company that you are writing about. To clarify, we do not store ANY passwords or sensitive information in clear text. Your assumptions are incorrect here. In the future if you have any questions or concerns you may ask us directly and we will explain further to alleviate your concerns. Thank you.
We didn’t really know what to make of that since it didn’t address the issue of the passwords not being stored in hashed form, instead only claiming that they were not stored in clear text, which isn’t the only way non-hashed passwords could be stored. So either the person didn’t really understand the issue at hand or they were trying to divert from the real issue.
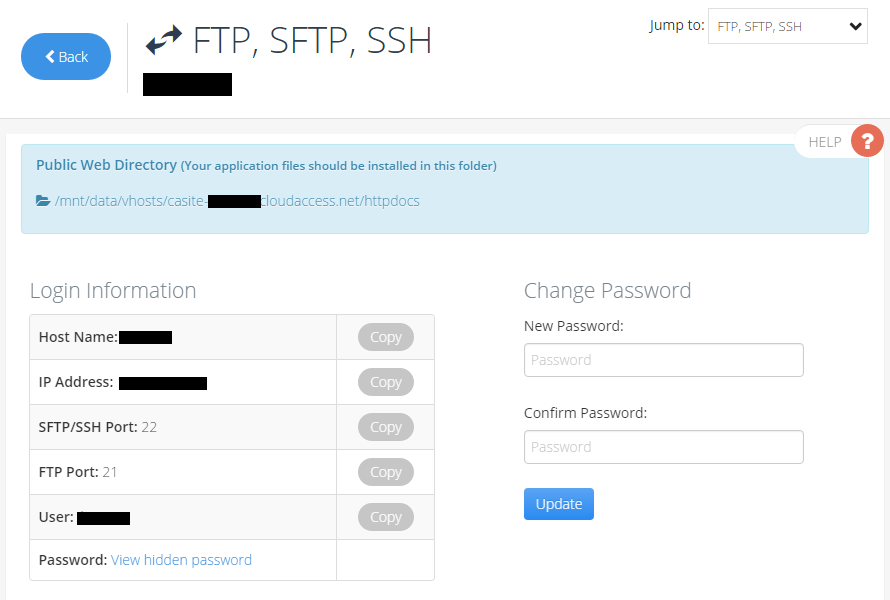
Whatever was the case there, the issue hasn’t been resolved as we were just working on a website hosted with CloudAccess.net and found that they are still storing the FTP/SFTP/SSH passwords in non-hashed form. You can see below that on the relevant page in their control panel there is still the option to view the password by clicking on “View hidden password”, which would not be possible if they were hashed: