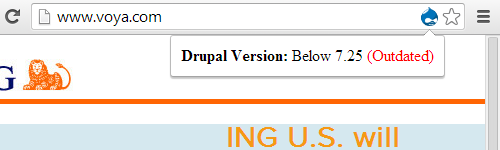
Yesterday, as part our series of posts highlighting the fact that even high profile websites are not taking the basic security measure of keeping the software running them up to date, we highlighted the fact that ING US was using outdated and insecure versions of Drupal on their website. Today we have a few quick follow-ups.
First it was brought to our attention that the fact that ING was using Drupal was a big enough deal for the creator of Drupal to highlight it, saying in part
You know when a piece of software is mature when it starts being adopted by financial services organizations.
The fact that such high profile user isn’t keeping Drupal up to date in light of the security need of doing so either means that that Drupal is too hard to keep up to date, which we strongly disagree with based on keeping our own installation up to date and handling plenty of upgrades for clients, or there is more general problem with security practices for websites.
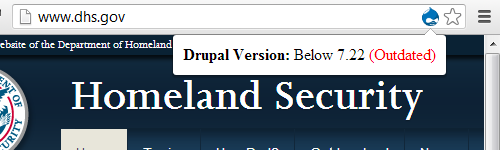
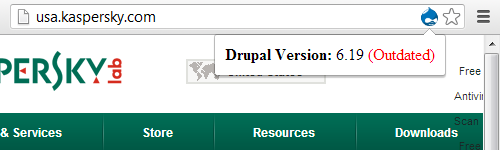
In the aforementioned post another ING US website was highlight as running Drupal and that website unfortunately has also not been kept up to date:
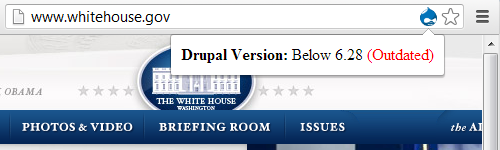
 That version is over two years and they have failed to apply five security updates (6.23, 6.27, 6.28, 6.29, and 6.30).
That version is over two years and they have failed to apply five security updates (6.23, 6.27, 6.28, 6.29, and 6.30).
At the bottom on that website is a link to a Web Site Security page, which in part advises keeping the software on your computer update:
Take care of your computer
-
Update your computer by installing the latest software and patches to prevent hackers or viruses from exploiting any known weaknesses in your computer.
It would great if ING, as well as everyone else running a website, took that advice and applied it to their websites.