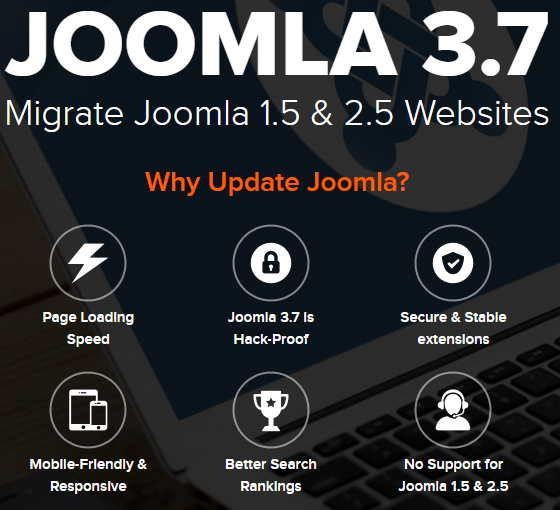
When it comes to bad information on the security of websites, far too often that information is coming from companies offering security services. A recent example we came across, while dealing with a hacked website, involved a Joomla focused web development company that in their marketing their service for upgrading or migrating to Joomla 3.7 claimed that Joomla 3.7 is “hack-proof”:
That certainly isn’t a claim that is made by Joomla (nor would you expect it to be a claim that is likely ever made by someone trying to be taken seriously).
Already a “high” priority SQL injection has been fixed since 3.7.0 was released, which was considered serious enough for Joomla to pre-announce that a security update was coming.
The same company offers to clean up hacked Joomla websites, so they should know better than to make that sort of claim and in fact they seem to understand that vulnerabilities continue to be found in Joomla based part of how they advertise that service:
We will identify possible loop hole in security and install required updates and patches. Because of consent Joomla and component upgrades, this is a critical step to prevent hacking.
In describing their service there was also this troubling claim:
As soon as we are engaged to fix your hacking issues or to prevent your website from hacking, we will do a thorough analysis and prepare an action plan to recover your website at the earliest. Mostly a Joomla upgrade should fix it, but it depends on the kind of website and problem you have.
We deal with lots of hacked Joomla websites and upgrading would not normally fix them. Perpetuating that idea is decidedly not helpful, as if our experience is any indication people with hacked website will often come to that conclusion and then hire someone to upgrade it without mentioning that they are doing that to clean up hack. Trying to upgrade a hacked website could actually make the situation worse, as it might cause the upgrade to go wrong and it could erase important evidence needed to determine how the website hacked, which may be needed to prevent it from being hacked again.