Recently we have been thinking that a way to help people to better understand why security is in such bad shape despite the amount of money spent on it, is to say to think of the security industry not as that, but as the “insecurity industry”. As security companies are not focused on improving security, but instead of making people believe that insecurity is inevitable and that they can provide protection, but not to the extent that people actually expect those companies to keep them things secure. A prime example of a company that would fit that description is SiteLock, which is a company that comes up often on our blog when it comes to bad practices of the security industry. The other day we had someone forward several messages they had received recently from them and part of one of those stood out:
Malware is a real problem that affects a lot of websites. It’s as prevalent as the common cold and can do some real damage if you don’t catch and treat it early.
So how will you know if your website gets infected with malware?
To help protect your website, your hosting provider has partnered with SiteLock to provide your website with a complimentary malware scanner. Every day this nifty little tool checks the first five pages of your website for malware, and sends you an alert if any is found.
Their idea of protecting websites isn’t making sure that websites are actually secure, which would prevent them from being infected with malware or otherwise hacked, but instead trying to detect the website is infected after being hacked and then offering services that still don’t secure the website. That is great way for them to make money, but it isn’t great for everyone else since websites can continually be hacked.
As that email indicates they are not alone in that, web hosts have partnered with them. Why would a web host partner with a company that isn’t focused on making sure their customers’ websites are secure? Well when it comes to what seems to be SiteLock’s biggest hosting partner, the Endurance International Group (EIG), a partial explanation is that the majority owners of SiteLock also run EIG. EIG also disclosed to investors at one time that they receive 55% of the revenue of services sold through their partnership. That creates a strong incentive for EIG to not provide the best security possible as that would mean less money for them and less money being made by another company owned by the people running EIG. It might explain, for example, why in the past we found that EIG was distributing known insecure versions of web software to their customers through one of the companies they own, MOJO Marketplace.
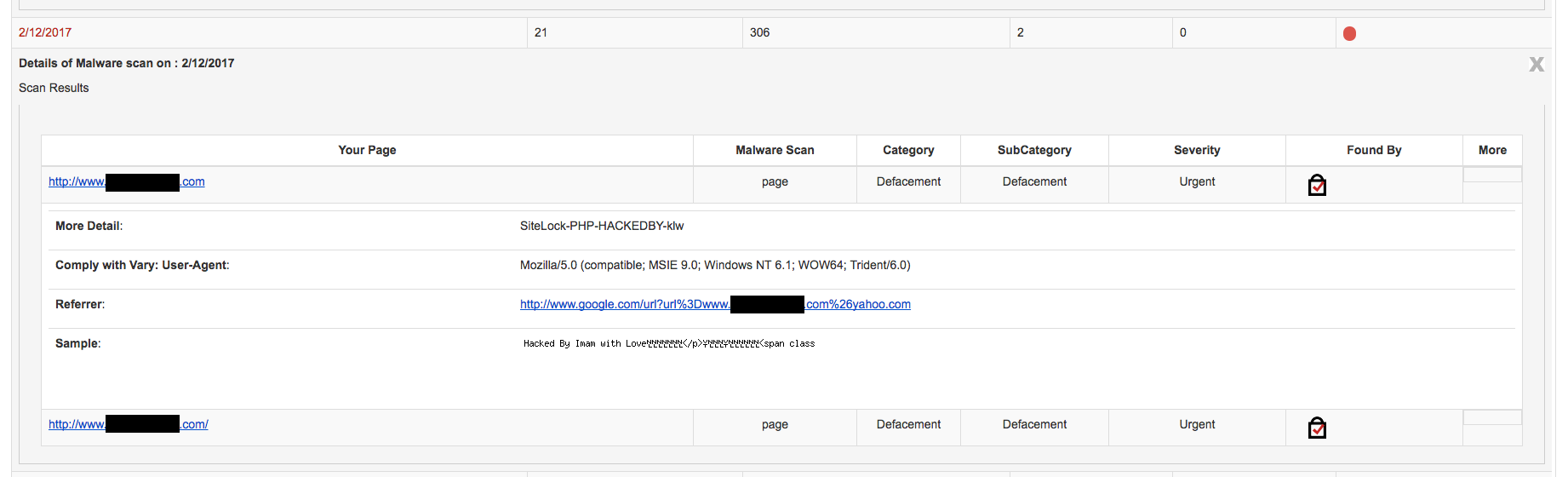
Over the years EIG has brought together numerous web hosting brands including A Small Orange, Bluehost, FatCow, HostGator, iPage, IPOWER, JustHost and quite a few others. The situation with a website hosted with HostGator that we cleaned up a hack on yesterday seems to be an example of where those incentives might have created a situation that doesn’t serve their customers well.
The website was hacked in way that it would serve spam pages with Japanese text to Google’s search crawler.
While you wouldn’t know it from many companies that cut corners when doing hack cleanups, one of the three basic steps in properly cleaning up a hacked website is to try to determine how it was hacked. With this website the files involved in the hack didn’t really seem to shed any light on that. The main piece of this hack involved code added to the index.php file of a WordPress installation that caused the code in a file at wp-confing.php to run, which would cause that code to run whenever the frontend of the website is accessed. That filename is similar to a legitimate WordPress file in the same directory, wp-config.php, which could indicate that the hacker has some knowledge of WordPress, but considering how popular it is, it doesn’t seem to be a good indication that the hack was anything WordPress related (we also didn’t find anything that was known to be insecure in the WordPress installation).
The hacker had also added the website to a Google Search Console account with the email address “xueqilve@gmail.com” and submitted a sitemap to get the spam pages added to Google’s index.
It looked like the malicious code causing the issue had been added a few days ago (though another file might have been there since November), so there still should have been logging available from when that occurred that would shed more light on the source of that. Unfortunately HostGator hadn’t had log archiving enabled by default in the website’s cPanel control panel, so we only had access to logging for the current day. That fact alone probably should tell you that the company doesn’t have much concern about security and it would be strange to not have that on if they had a legitimate partnership with a security company since that would be an obvious thing to do because of its importance for dealing with hacked websites.
As we have found though, SiteLock usually doesn’t attempt to determine how a website was hacked, so they wouldn’t have a need for that logging. Considering that they don’t usually do that, it makes it not all that surprising that services they offer to protect website don’t work well, since they don’t know how websites are actually being hacked.
We did have one last lead to follow in trying to get some idea of how the website was hacked. In the root directory of the website there was a file named bray.php that contained the following message:
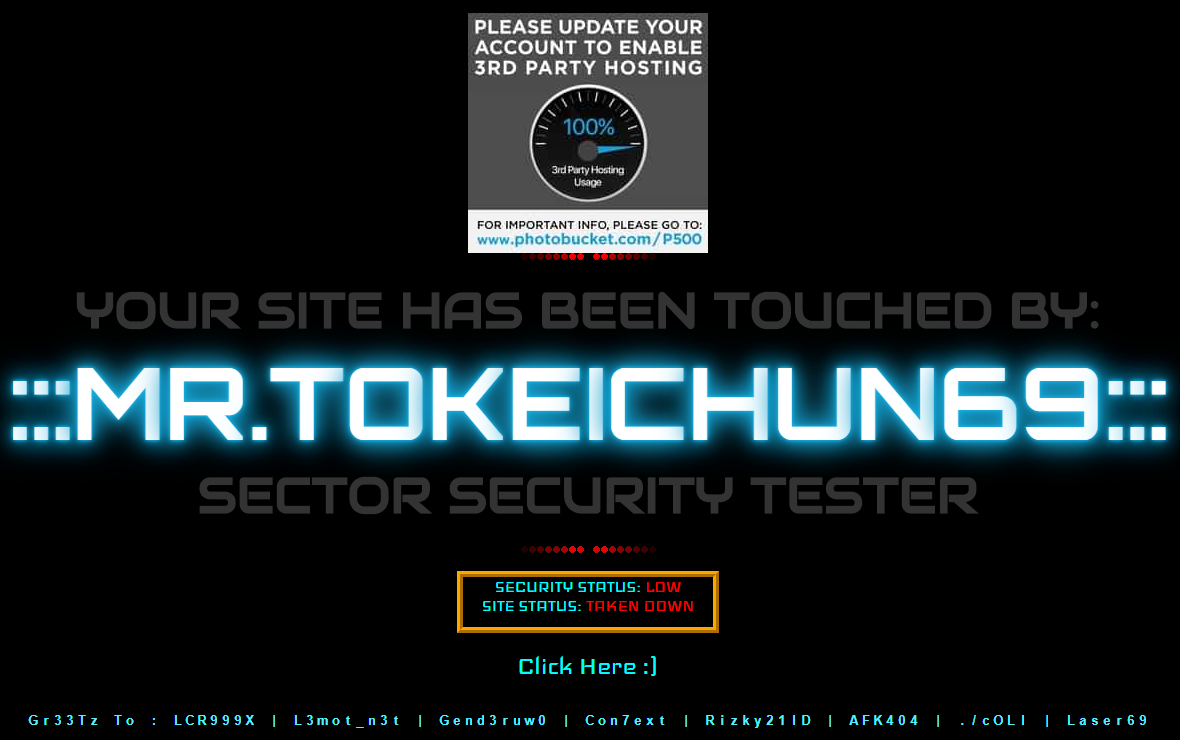
Hacked By Isal Dot ID
Through the website Zone-H, which catalogs defaced websites, we could see that same file had been placed on numerous websites recently. In looking over a number of those websites what stood out was that they all were hosted with HostGator or other EIG brands. Here are examples of websites hit at several nearly sequential IP address registered to HostGator:
If a hacker was hacking websites through a vulnerability in a WordPress plugin for example, that isn’t what you would expect to see, instead you should see websites hosted with numerous different web hosts.
At best you have a situation where a hacker looks to be specifically targeting numerous websites at EIG brands. There is also the possibility they are taking advantage of some security issue on EIG’s end to hack the websites.
Even if they are just targeting website hosted with EIG brands that seems like something that the hosting company would want to investigate and try to prevent as much as possible. That doesn’t seem to be the case here because later yesterday we were contacted by someone else with the exact same hack. They said HostGator has only been interested in pushing SiteLock. When you understand the incentives involved, it really isn’t surprising that is happening.
Update March 19, 2018: We have now come across a article from year ago in which the hacker behind this, claimed to have had full access to a server that contained another website they had hacked. That website was hosted with HostGator at the time (and Bluehost now). While the claim of a hacker isn’t necessarily reliable, it does raise further suspicion that there may be a security issue on EIG’s end