We are often brought in to re-clean hacked websites after another provider, Sucuri, has been hired to clean them, but has intentionally cut corners, leading to the website still being hacked after they have claimed to have cleaned it up. In the most recent instances we were brought in, the website was still hacked, though to a more limited extent than usual. But what stood out more that not only was the website still also insecure, but it was still insecure because of Sucuri’s parent company, GoDaddy. That is something Sucuri would have noticed if they have done one of three key components of a proper cleanup, trying to determine how the website was hacked and fixing that.
What makes the lack of doing that stand out more, is that an email sent out by Sucuri after their cleanup made this claim:
Out of date software is the most common cause of website compromise. It’s highly recommended to get that updated as soon as you can.
So clearly they believe you can determine how websites are hacked, but they don’t do that. Beyond that being a problem to get things properly cleaned, it also would it make hard for something they claim to do right at the top of their home page, namely preventing future attacks:
We fix hacks and prevent future attacks.
How do you prevent future attacks if you don’t know how previous ones were actually done? In other instances we were brought in, the website was already using Sucuri’s service when they were hacked, so clearly their prevention didn’t work, but Sucuri wasn’t interested in figuring out what went wrong.
GoDaddy’s Insecure Hosting
The remaining piece of the hack that they missed were admin accounts for the website created by a hacker or hackers. Looking in to how those got there would be part of trying to determine how the website was hacked. If you actually do that work regularly, as we do, then what you immediately notice is that the accounts don’t look like they were created through the normal process in the software being used on the website, since most of the details, like when the accounts were registered, were empty. What that usually means is the hacker had direct access to the website’s database.
If the hacker had access to the database, that most likely mean they were able to get access to the credentials for the database. A type of vulnerability that could provide them with that information is one that is widely exploited when it exists in software. We rarely see websites that have been hacked due to that type of vulnerability, because in most cases the hacker doesn’t have a way to directly connect to the database to then use the credentials.
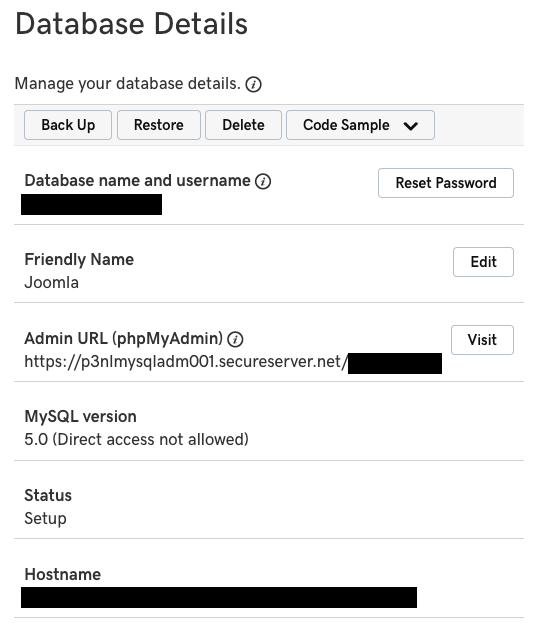
With this website, though, we confirmed that you could remotely connect to the database. The vast majority of websites don’t need to the database to be remotely accessible and they normally are not, since it introduces a security risk with no upside for almost all websites. Fixing that would be something that Sucuri should have done, if they were doing things properly instead of cutting corners. When we went to see about doing that we found it was already supposed to be the case, as the database wasn’t supposed to be able to be connected to remotely:
It wasn’t a one off issue, as another part of the work Sucuri failed to do was to update the software on the website. When went to work on that we created an additional database to test the upgrade and it was also remotely accessible despite being set to not be.
That wasn’t the only security issue we ran across with the hosting account, as we will discuss in a future post.
What really stands out is the website is hosted by GoDaddy, which owns Sucuri. Is it any wonder that security is so bad, when not only does a security company not do the basic work they should do, not only is a web host failing on basic security, but when the two are part of the same company.