Recently, while searching for some information about another security company an ad for SiteLock also showed up in the search results:
The page linked to in the ad seems worth discussing as to what it says about the SiteLock’s view of website security (which is line with plenty of other companies as well), but the ad itself had a number of claims that stood out to us as well.
For example, based on everything we have seen SiteLock charges incredibly high prices (and not all in line with level of service you are getting), so the idea you are getting the “lowest price” seems laughable.
It also claims that you can “Switch to SiteLock for Free.”, which seems meaningless, as unless some other service charges you an extra fee if you previously used another service, there wouldn’t be a fee for switching. If you click the ad the only thing listed as being free is getting a quote (would someone else charge for a quote?).
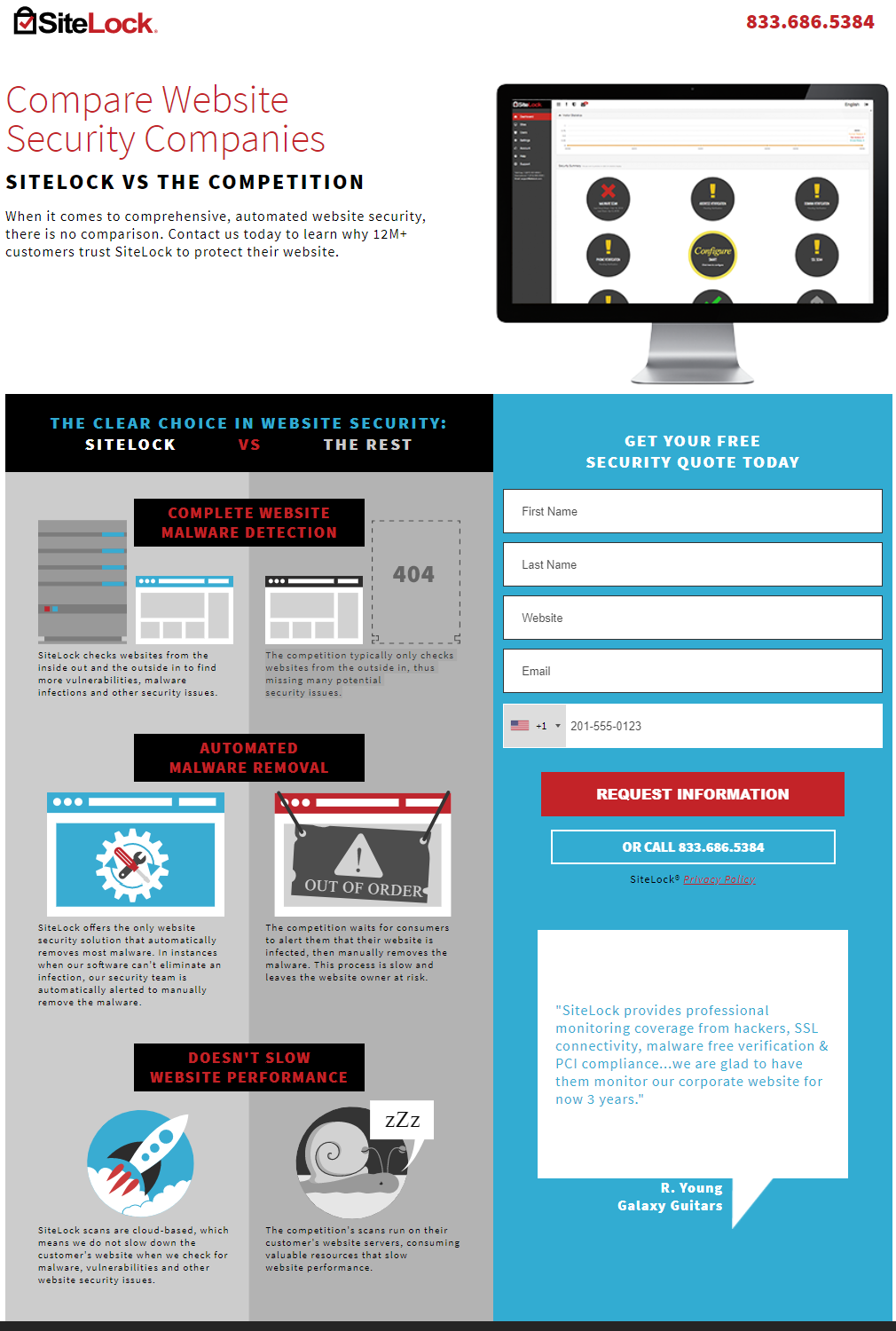
The claims about “Ditch the Weak Security” and “the only fully automated website security” touch on what is seen on the page you are taken to when clicking the ad:
In that SiteLock claims there is no comparison between them and others when it comes to website security:
When it comes to comprehensive, automated website security, there is no comparison.
But in looking at the things they are comparing it shows they are not really all that focused on actually securing websites:
- COMPLETE WEBSITE MALWARE DETECTION
- AUTOMATED MALWARE REMOVAL
- DOESN’T SLOW WEBSITE PERFORMANCE
If a website is secured there wouldn’t be any malware to be detected or removed in the first place. As we were just discussing yesterday with a real world example involving another well known security company, automated attempts to do both of those things don’t look to work very well either.
The details of those things being compared are either missing any evidence for claims as to SiteLock’s superiority (which seems like a basic and important part of a comparison) or don’t make sense.
For the first item they claim to “find more vulnerabilities, malware infections and other security issues” than anyone else:
SiteLock checks websites from the inside out and the outside in to find more vulnerabilities, malware infections and other security issues.
But no evidence is provided to back that up.
When it comes to vulnerabilities, in the past we have written about how we couldn’t find evidence that they vulnerability scanner was actually detecting vulnerabilities, much less more of them than anyone else. We later found that their vulnerability scanning looks to be at least, maybe only, running a tool called Nessus over websites, which causes some serious problems.
Next up is the claim about their malware removals:
SiteLock offers the only website security solution that automatically removes most malware. In instances when our software can’t eliminate an infection, our security team is automatically alerted to manually remove the malware.
There are a couple of obvious issues with that. First, they are not the only ones with automated malware removal. Second, when cleaning up a hack you don’t want to just remove it, as that alone does nothing to fix the vulnerability that allowed it to happen in the first place. So they are promoting that they improperly clean up websites, while making it sound like a good thing.
The final one doesn’t really make sense. They claim this about their service:
SiteLock scans are cloud-based, which means we do not slow down the customer’s website when we check for malware, vulnerabilities and other website security issues.
They claim this about their competitors:
The competition’s scans run on their customer’s website servers, consuming valuable resources that slow website performance.
But prior to that they claimed this about their competitors:
The competition typically only checks websites from the outside in, thus missing many potential security issues.
It doesn’t make sense that the competitors are checking “websites from the outside in”, but that their “scans run on their customer’s website servers”. In any case SiteLock is clearly going to use some resources to scan the websites, since they have to access them somehow to do that checking.
12M+ Customers
The claim on the page that “12M+ customers trust SiteLock to protect their website” is something we should take up more in detail sometime, as it is great example of SiteLock’s ridiculous claims. But a quick example of why that is ridiculous is that 6 million of that customer count come from their purchase of a company named Patchman. That company provides a service for web hosts that would patch some security vulnerabilities in some software used on their customers websites. That company doesn’t have 6 million customers, instead that is a claimed count all of the customers of the web host they do business with had. So half of SiteLock’s customers count are not necessarily even aware of the service being provided, much less to trust it to protect them. It also would provide limited protection since it only deals with some security issues and in the case of WordPress, the developers of WordPress already release security updates for older versions, so the service duplicates protection already provided.
Securing Your Website
If your website hasn’t been hacked what you should focus on is making sure you are doing the basics of security since those will actually help protect your website. If you are looking for a security service in addition to that, we would recommend you only use one that provides evidence from independent testing that they are effective at doing that. We should note that we have yet to see a company that provides that (or even presents evidence from non-independent testing to that effect).
If your website has been hacked you want to make sure to get it properly cleaned up, which involves removing anything the hacker added to the website, securing the website (which usually involves upgrading the software on it), and trying to determine how the website was hacked and fixing that. Many companies, including SiteLock, cut corners, as can be seen SiteLock by touting that they don’t do things properly. So simply going with a well known company doesn’t mean that you are going to get a good result, in fact what we have seen is that the biggest names are usually very bad at security (lying about things has been effective method to make security companies popular, but it doesn’t help to make them good at security).
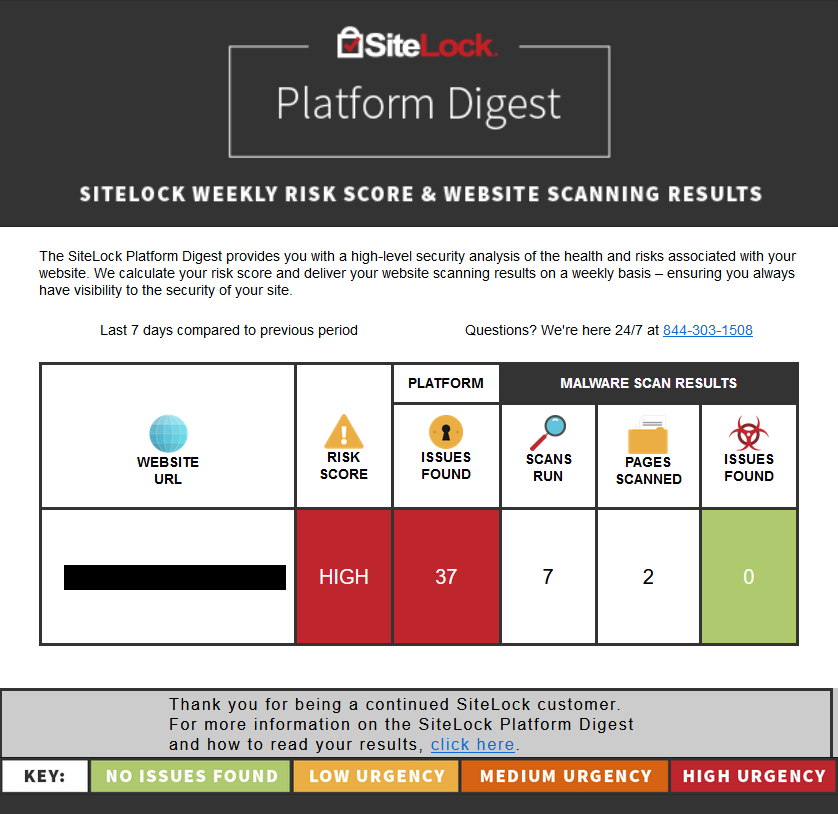
Is SiteLock Making Websites Less Secure?
Recently we have run across evidence that SiteLock and their owners might actually be making websites less secure. While cleaning up a hacked website last week we noticed that at of one of SiteLock’s hosting partners, the Endurance International Group (which does business through brands A Small Orange, Bluehost, FatCow, HostGator, iPage, IPOWER, JustHost and quite a few others), a hacker has at least been targeting websites hosted by them or more concerning, the hacker isn’t so much as targeting websites hosted by them, but taking advantage of security issue with Endurance to gain access to their customer’s websites. You would think a web host would be interested in looking into something like that, but instead when contacted about hacked websites they just push people to hire SiteLock to clean up the websites, which does nothing to deal with the source of the hackings. Part of the reason for them doing that is that the Endurance gets the majority of the revenue for SiteLock services sold through their partnership, so they have a financial interest not to make their hosting as secure as possible. Another reason for pushing SiteLock is that the majority owners of SiteLock also run Endurance.
The very real possibility that the owners of a security company are also run a web hosts that is the cause of their customers being hacked is on the one hand kind of stunning, on the other hand it is in line with what we have come to expect when it comes to the handling of the security of websites.